— Today and Beyond.
Discover how IT Security C&T empowers organizations with end-to-end cybersecurity services, from strategy and architecture to managed detection and AI-driven defense.
Explore our complete range of solutions designed to protect your data, your systems, and your future.

Strategy and Transformation
We help organizations build and execute cybersecurity strategies that align with business objectives—driving transformation, maturity, and resilience across all digital operations. and the following subservices:
- Strategy Development & Execution
- Cybersecurity Transformation
- Program Management & Capability Building

Enterprise Security Architecture
We design secure, scalable, and adaptive enterprise architectures based on global frameworks like SABSA, Zero Trust, and TOGAF to strengthen your security posture from the ground up. and the following subservices:
- Design-by-Principle
- SABSA
- Zero Trust and Security Adapted TOGAF
GRC Consultation
Our GRC experts support organizations in building governance, risk, and compliance frameworks that meet international and national standards—ensuring visibility and control across the enterprise.
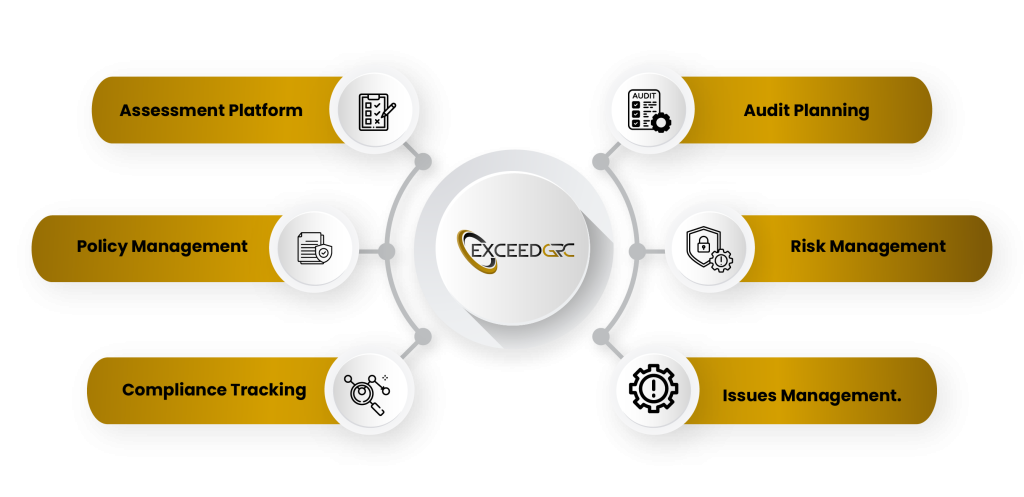
ExceedGRC Platform
Our in-house ExceedGRC platform simplifies risk, policy, and compliance management through automation, reporting, and integrated dashboards.

Data Protection
We secure your organization’s most critical asset—data—through advanced protection frameworks covering governance, classification, and preventive controls.
- Data Governance
- Data Management
- Data Classification
- Data Loss Prevention
- Digital Rights Management
- File Integrity Monitoring

Data Privacy
We enable organizations to comply with privacy laws and build trust with customers through effective data privacy programs and regulatory alignment.
- Data Privacy Compliance
- Privacy Impact Assessment
- Data Protection Impact Assessment
- Record of Processing Activities
- Data Subject Requests
- Usage & Consent Management
Identity & Access Management
We ensure the right people have the right access at the right time by implementing comprehensive IAM frameworks and privileged access controls.
OT/ICS Cybersecurity
We safeguard industrial environments by protecting operational technology (OT) and industrial control systems (ICS) through secure architectures, monitoring, and vendor access management.


Attack Surface Reduction
We proactively discover and remediate vulnerabilities before attackers do—reducing exposure through continuous assessment and advanced red-teaming operations.
- Assessment
- Penetration Testing
- Red-Teaming
- Technical Architecture Review
- Breach Simulation
- Social Engineering
- Brand Protection
- Compromise Assessment
- Configuration Review
- Source Code Review
- Vulnerability Remediation

Managed Detection and Response
Our 24×7 MDR service combines advanced monitoring, threat intelligence, and incident response to detect and contain cyber threats in real time.
- 24×7 Monitoring
- SIEM Solution Content Engineering
- Threat Intelligence platform Integration
- Threat Modelling
- Incident Response
- SOAR
- SecOps
- Digital Forensics
- Malware Analysis & Reverse Engineering

Workload Security
We protect applications and workloads across on-premises and cloud environments through secure coding, DevSecOps, and modern container security practices.
- Application Security
- SecDevOps
- API Security
- Cloud Security
- Container Security
- Virtualization
- Microsegmentation
- Mobile App Security.

Infrastructure Security Professional Services
Our experts deliver end-to-end implementation and hardening of security infrastructure to protect networks, endpoints, and critical systems.
- Professional Services For Firewalls
- DNS Protection
- DDoS Protection
- HSM Appliances
- Database Activity Monitoring
- CASB
- CSPM
- EDR
- XDR
- NDR

IoT and IIoT Protection
We design secure frameworks for IoT and industrial IoT ecosystems, ensuring device integrity, safe communication, and compliance with emerging technologies.
- Secure Design Authority
- Asset Management
- Use Cases
- Protocols
- Sensors
- Firmware Upgrades
- IIoT zones & Conduit Protection Levels
- Embedded Device Communication Integrity
- Integration & Emerging Technologies

Enterprise Resilience
We prepare your business to withstand and recover from disruptions through integrated continuity, crisis, and recovery management programs.
- Business continuity management
- Disaster Recovery
- Crisis Management
- Emergency Response
- Scenario Planning & Drills

Training and Awareness
We empower teams with practical knowledge, simulations, and certifications that build cybersecurity competence and awareness at every organizational level.
- Competency Management
- Training Needs Analysis
- Certification
- Accreditation
- Cyber Drill Simulations
- LMS
- Phishing
- Social Engineering

Capability Call-off Agreements
We provide on-demand access to experienced cybersecurity professionals through flexible engagement models tailored to your operational needs.
- Staff Augmentation
- Cybersecurity Professionals as a Service (CPaaS)
- vCISO
AI Security
We pioneer trusted and secure AI implementation by integrating AI-driven threat defense and responsible model management frameworks.
Our experts are ready to help you identify, assess, and strengthen your cybersecurity posture.
Fill out the form below and we’ll contact you with tailored insights or consultation options based on your business needs.